> security 100%,
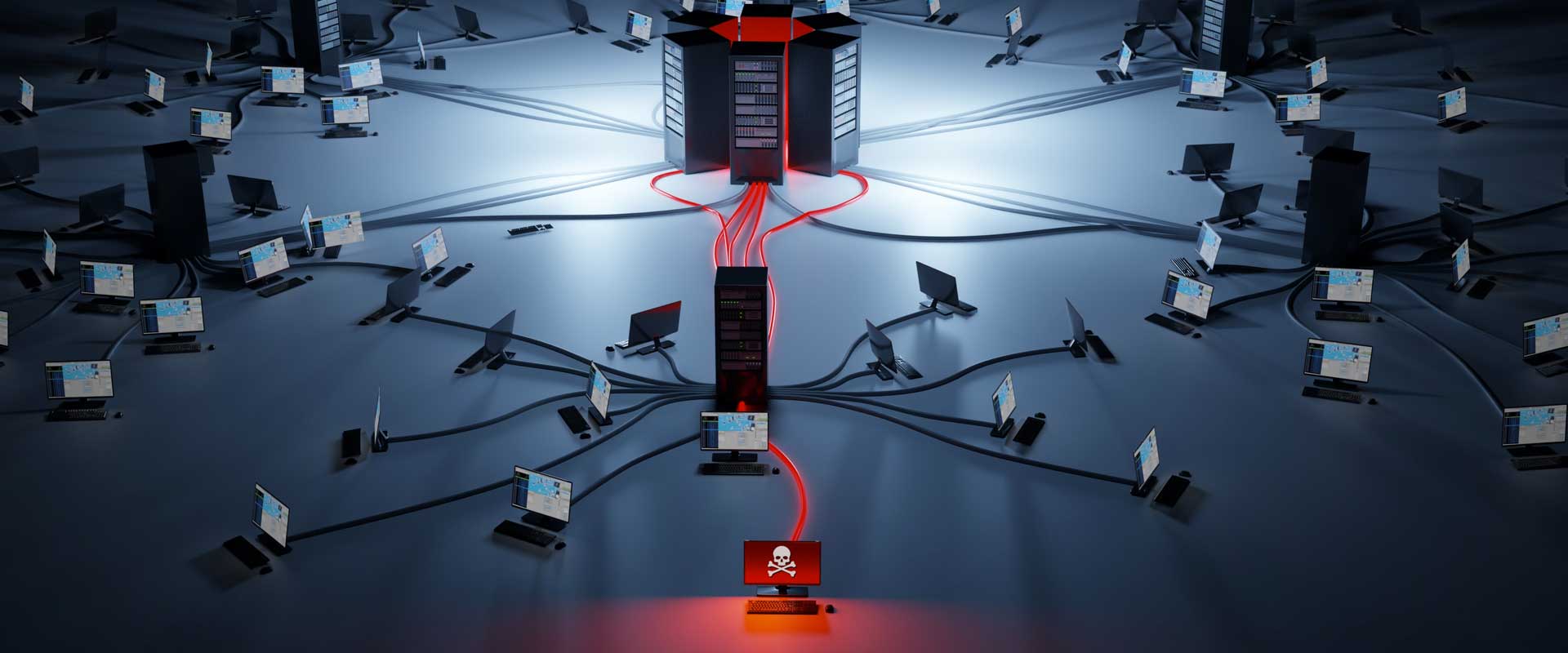
The prevention from vulnerabilities:
Vulnerability Assessment is the first step that allows you to preview what may be the weaknesses of your work environment. It allows you to verify the level of global defence of your IT system. Penetration Test is the second step that exploits the vulnerabilities identified in the previous phase (VA) simulating a cyberattack by an ethical hacker to demonstrate the existence of the weaknesses and the level of risk to which the business is exposed to.
Vulnerability Assessment
Penetration Test
Web Application Analysis
Ethical Hacking Services
Red Teaming
Industrial Network Assessment
WiFI Wardriving
Data Loss Prevention
SIEM Solutions
Mobile Device Management
> Vulnerability assessment, demonstration, and mitigation
It is an essential requirement – but not enough – in the long process of an IT infrastructure empowerment for both big corporate organisations and SMEs.
This activity wants to raise awareness identifying the real risks and damages of an attack and then to be able to build the appropriate defence strategy for your company employing the skills of our experienced and OSCP certified personnel.

Knowing your planet is a step
towards protecting it
– Jacques Yves Cousteau
> Ask for informations
>OUR LOCATIONS
MODENA Never stops
Via Grazia Deledda, 38
41043 Formigine (MO) – Italy
Tel: +39 059 5961 333
info@ftpsrl.it

PESARO Never stops
Via Bruno Bedosti, 21
61122 Pesaro (PU) – Italy
Tel: +39 0721 1838 555
info@ftpsrl.it

PIACENZA Never stops
Via Rinaldo Ancillotti, 8
29122 Piacenza (PC) – Italy
PIVA e CF 01429880337
info@ftpsrl.it

